docker安装几个常用应用
发布时间 : 2021-08-02 14:15
几点心得: 1、在nginx的反向代理中,如果有两个子域名指向同一个服务,则无法打开
一、创建网络 mynet ,作用:之后可以通过容器名连接相应容器 1 2 3 docker network create mynet docker network ls
二、安装Portainer 1.停止旧的容器 2.删除旧的容器 3.删除旧的镜像 1 docker rmi portainer/portainer-ce
4.拉取新的镜像,注意portainer从2.0.0版本镜像名字改为portainer/portainer-ce 1 docker pull portainer/portainer-ce
5.使用新的镜像启动新的容器 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 docker volume create portainer_data docker run -d -p 8000:8000 -p 9000:9000 --net='mynet' --name=portainer --restart=always -v /var/run/docker.sock:/var/run/docker.sock -v portainer_data:/data portainer/portainer-ce docker run -d -p 8000:8000 -p 9000:9000 --net='mynet' --name=portainer --restart=always -v /var/run/docker.sock:/var/run/docker.sock -v /opt/docker-data/portainer:/data portainer/portainer-ce docker run -d \ --name=portainer \ --hostname docker-portainer \ --net='yle-web' \ -p 8000:9000 \ --restart=always \ -v /var/run/docker.sock:/var/run/docker.sock \ -v /volume1/docker/portainer:/data \ portainer/portainer-ce:latest docker run -d \ --name=portainer \ --hostname docker-portainer \ --net='net-yle-test' \ --restart=always \ -v /var/run/docker.sock:/var/run/docker.sock \ -v /root/docker-data/portainer:/data \ portainer/portainer-ce:latest -p 8000:9000 \
6.用portainer远程管理其他机器上的docker 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 vi /usr/lib/systemd/system/docker.service ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock -H tcp://0.0.0.0:2375 ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock -H tcp://0.0.0.0:2376 --tlsverify --tlscacert=/opt/docker-data/docker-ca/ca.pem --tlscert=/opt/docker-data/docker-ca/server-cert.pem --tlskey=/opt/docker-data/docker-ca/server-key.pem systemctl daemon-reload & systemctl restart docker curl -L https://downloads.portainer.io/agent-stack.yml -o agent-stack.yml && docker stack deploy --compose-file=agent-stack.yml portainer-agent docker swarm init root@LS-GitLab:~# netstat -tnlp |grep 2375 tcp6 0 0 :::2375 :::* LISTEN 15462/dockerd ps -ef | grep docker
Tls 远程控制
https://docs.docker.com/engine/security/protect-access/
解决思路 :创建 docker-tls.sh,并执行
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 SERVER="10.10.10.51" PASSWORD="lyou" COUNTRY="CN" STATE="ZJ" CITY="HZ" ORGANIZATION="ilab" ORGANIZATIONAL_UNIT="ilab" EMAIL="test@gmail.com" echo "开始生成文件" openssl genrsa -aes256 -passout "pass:$PASSWORD " -out ca-key.pem 4096 openssl req -new -x509 -passin "pass:$PASSWORD " -days 365 -key ca-key.pem -sha256 -out ca.pem -subj "/C=$COUNTRY /ST=$STATE /L=$CITY /O=$ORGANIZATION /OU=$ORGANIZATIONAL_UNIT /CN=$SERVER /emailAddress=$EMAIL " openssl genrsa -out server-key.pem 4096 openssl req -subj "/CN=$SERVER " -new -key server-key.pem -out server.csr sh -c 'echo "subjectAltName = IP:' $SERVER ',IP: 0.0.0.0" >> extfile.cnf' sh -c 'echo "extendedKeyUsage = serverAuth" >> extfile.cnf' openssl x509 -req -days 3650 -in server.csr -CA ca.pem -CAkey ca-key.pem -passin "pass:$PASSWORD " -CAcreateserial -out server-cert.pem -extfile extfile.cnf openssl genrsa -out key.pem 4096 openssl req -subj '/CN=client' -new -key key.pem -out client.csr sh -c 'echo extendedKeyUsage = clientAuth >> extfile.cnf' openssl x509 -req -days 3650 -in client.csr -CA ca.pem -CAkey ca-key.pem -passin "pass:$PASSWORD " -CAcreateserial -out cert.pem -extfile extfile.cnf chmod 0400 ca-key.pem key.pem server-key.pemchmod 0444 ca.pem server-cert.pem cert.pemrm -rf ca.srl server.csr client.csr extfile.cnfecho "生成文件完成"
配置Docker支持TLS
1 vim /usr/lib/systemd/system/docker.service
修改以ExecStart开头的配置,开启TLS认证,并配置好CA证书、服务端证书和服务端私钥,修改内容如下;
1 ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock -H tcp://0.0.0.0:2376 --tlsverify --tlscacert=/root/docker-data/docker-ca/ca.pem --tlscert=/root/docker-data/docker-ca/server-cert.pem --tlskey=/root/docker-data/docker-ca/server-key.pem
重启Docker服务,这样我们的Docker服务就支持使用TLS进行远程访问了!
1 systemctl daemon-reload && systemctl restart docker
接下来我们将使用docker-maven -plugin来打包Docker镜像,使用的代码为原来的mall-tiny-docker例子。
1 2 3 4 [ERROR] Failed to execute goal com.spotify:docker-maven-plugin:1.1.0:build (build-image) on project mall-tiny-docker: Exception caught: com.spotify.docker.client.shaded.com.fasterxml.jackson.databind.exc.MismatchedInputException: Cannot construct instance of `com.spotify.docker.client.messages.RegistryAuth` (although at least one Creator exists): no String-argument constructor/factory method to deserialize from String value ('desktop' ) [ERROR] at [Source: UNKNOWN; line: -1, column: -1] (through reference chain: java.util.LinkedHashMap["credsStore" ]) [ERROR] -> [Help 1] 123
修改完版本后打包,发现TLS不再支持http了,需要改用https,修改配置为https;
1 2 [ERROR] Failed to execute goal com.spotify:docker-maven-plugin:1.2.2:build (build-image) on project mall-tiny-docker: Exception caught: Request error: GET http://192.168.3.101:2375/version: 400, body: Client sent an HTTP request to an HTTPS server. HTTP 400 Bad Request -> [Help 1] 1
修改完成后再次打包,继续失败,需要添加对应的客户端证书才能访问;
1 2 [ERROR] Failed to execute goal com.spotify:docker-maven-plugin:1.2.2:build (build-image) on project mall-tiny-docker: Exception caught: java.util.concurrent.ExecutionException: com.spotify.docker.client.shaded.javax.ws.rs.ProcessingException: javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target -> [Help 1] 1
将如下文件复制到指定目录,这里复制到了I:\developer\env\docker-ca;
1 2 3 4 5 6 7 8 9 10 ca.pem CA证书 cert.pem 客户端证书 key.pem 客户端证书私钥 123 docker --tlsverify \ --tlscacert=ca.pem \ --tlscert=cert.pem \ --tlskey=key.pem \ -H=10.10.10.51:2376 version
参考文档:https://zhuanlan.zhihu.com/p/149235759
查看防火墙状态
1 >systemctl status firewalld
开启防火墙
1 >systemctl start firewalld
关闭防火墙
1 >systemctl stop firewalld
查看当前firewall状态
重启firewall
禁止开机启动
1 >systemctl disable firewalld.service
查看已经开放的端口:
1 >firewall-cmd --list-ports
开启端口
1 >firewall-cmd --zone=public --add-port=80/tcp --permanent
命令含义:
–zone #作用域
–add-port=80/tcp #添加端口,格式为:端口/通讯协议
–permanent #永久生效,没有此参数重启后失效
开启端口后需要重启防火墙
三、搭建个性导航页 1 2 3 4 docker run -d --name home-page --net='mynet' -p 8888:8080 -v /opt/docker-data/home-page/www:/var/www/html --restart unless-stopped quchaonet/2048 docker run -d --name music-player --net='mynet' -p 8264:264 -v /opt/docker-data/music-player/cache:/var/www/html/cache oldiy/music-player-docker
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 docker run -d \ --name=heimdall \ --hostname docker-heimdall \ --net='mynet' \ -e TZ=Asia/Shanghai \ -p 8081:80 \ -p 8843:443 \ -v /opt/docker-data/heimdall/config:/config \ -v /opt/docker-data/heimdall/www:/var/www/localhost/heimdall \ --restart unless-stopped \ lscr.io/linuxserver/heimdall docker run -d \ --name=heimdall \ --hostname docker-heimdall \ --net='net-sxmj' \ -e PUID=1000 \ -e PGID=1000 \ -e TZ=Asia/Shanghai \ -v /root/docker-data/heimdall/config:/config \ --restart unless-stopped \ lscr.io/linuxserver/heimdall
1 2 3 4 5 6 7 8 9 10 11 12 13 14 docker run -d \ --name hoppscotch \ --hostname docker-heimdall \ --net='net-yle-test' \ -e TZ=Asia/Shanghai \ hoppscotch/hoppscotch:latest docker run -d \ --name hoppscotch \ --hostname docker-heimdall \ --net='net-yle-test' \ -e TZ=Asia/Shanghai \ -v /root/docker-data/postman:/app \ hoppscotch/hoppscotch:latest
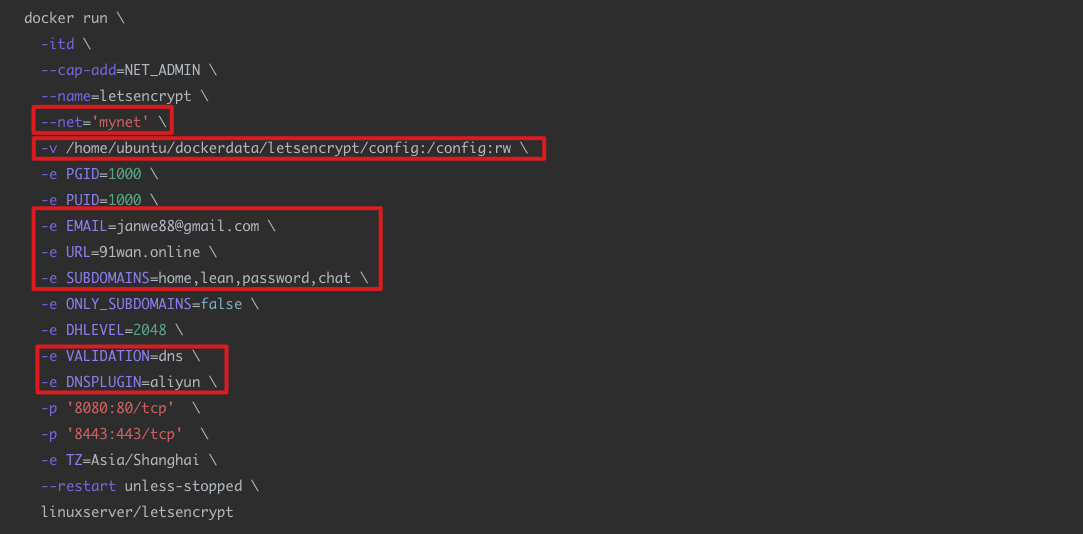
四、安装letsencrypt,作用:用于反向代理
PGID,PUID 可在终端运行 id 命名获取
1、先创建容器
红框中为需要根据自己做修改
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 docker run \ -itd \ --cap-add=NET_ADMIN \ --name=letsencrypt \ --hostname=docker-letsencrypt \ --net='mynet' \ -v /opt/docker-data/letsencrypt/config:/config:rw \ -e PGID=0 \ -e PUID=0 \ -e EMAIL=janwe88@gmail.com \ -e URL=91wan.online \ -e SUBDOMAINS=home,lean,password,dell,portainer,svn,blog,synology \ -e ONLY_SUBDOMAINS=true \ -e DHLEVEL=2048 \ -e VALIDATION=dns \ -e DNSPLUGIN=aliyun \ -p '6080:80/tcp' \ -p '6443:443/tcp' \ -p '6389:3389/tcp' \ -e TZ=Asia/Shanghai \ --restart unless-stopped \ linuxserver/letsencrypt
2、停止刚新建的容器,因为还需要配置相关aliyun信息 1 2 3 4 5 docker ps docker stop contain_id
3、配置aliyun信息,修改 /home/ubuntu/dockerdata/letsencrypt/config/dns-conf/aliyun.ini 1 2 3 4 5 6 certbot_dns_aliyun:dns_aliyun_access_key = aaaaa certbot_dns_aliyun:dns_aliyun_access_key_secret = bbbbb
4、在软路由上配置 动态dns
用户登录名称 dns@
5、启动容器 1 2 3 4 5 docker start contain_id docker logs -f contain_id
6、设置端口转发 注:OpenWRT中的 防火墙》端口转发,可能是存在 nat回环的问题,设置之后会导致 外网可能通过 域名:端口 访问,但内网不可能访问
研究了两天才找到解决的方法:用Socat设置端口转发
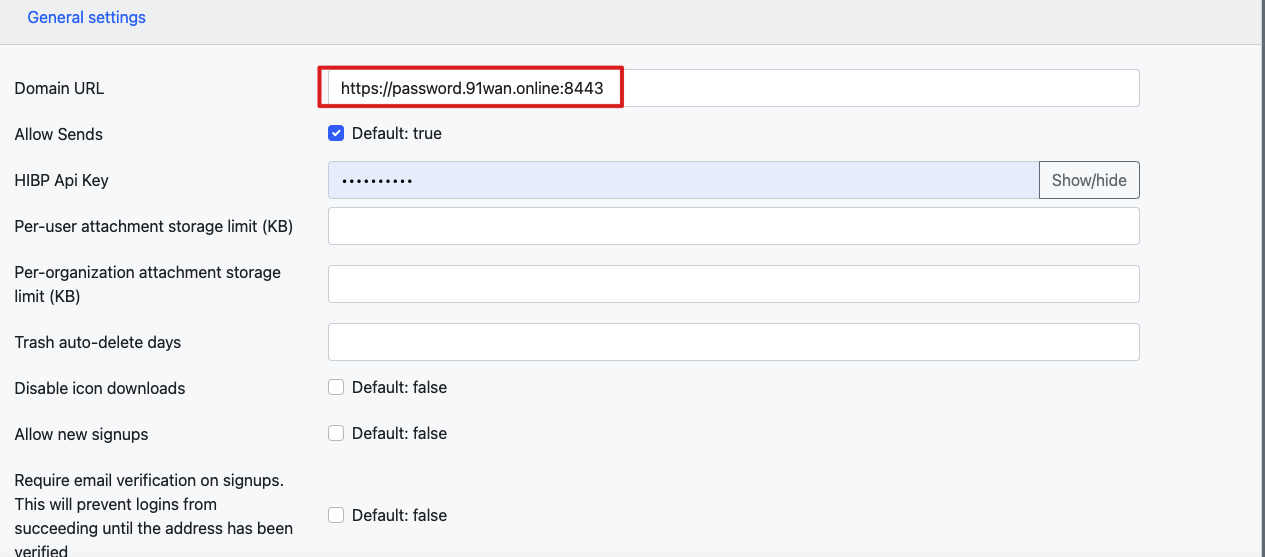
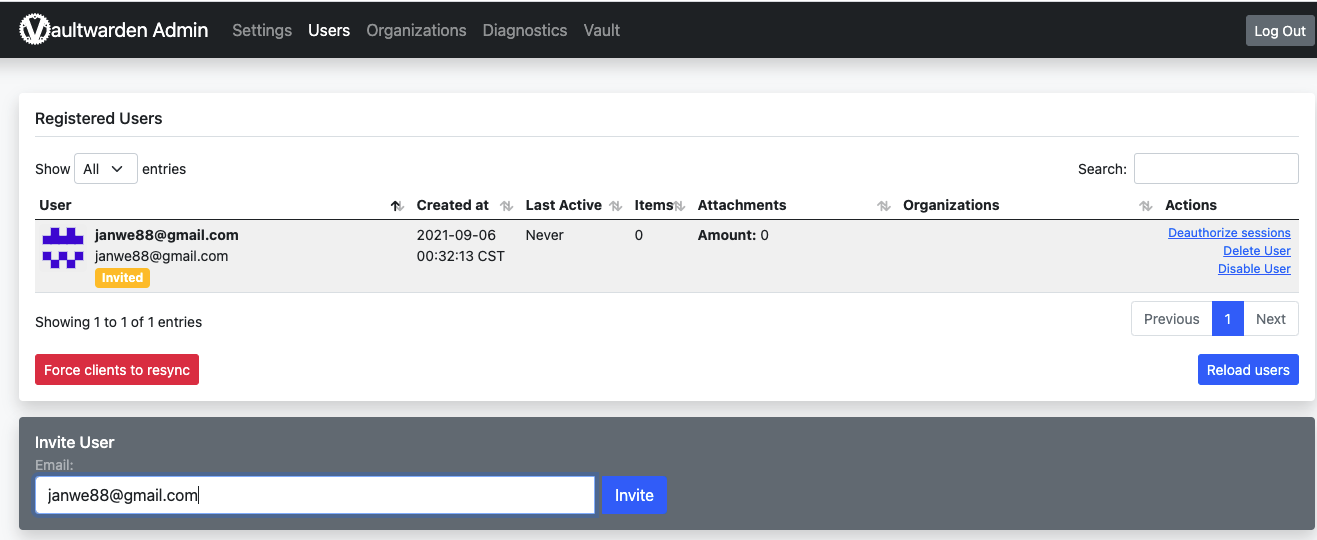
五、安装 vaultwarden,用于存储密码 1、创建容器 注:如果是exsi安装的虚拟机,需要先设置虚拟机时区,否则设置 两步验证后无法登录 1 2 3 4 tzselect cp /usr/share/zoneinfo/Asia/Shanghai /etc/localtimedate -Rreboot
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 openssl rand -base64 48 eSLg6ZvXUjcd87Oiq2MRpTJEb0uODm4doh/RJSYi+GQeV7tCs+GP8l/98EEQ8mYf docker run -itd \ -e PGID=0 \ -e PUID=0 \ --name='vaultwarden' \ --net='mynet' \ -e TZ="Asia/Shanghai" \ --restart unless-stopped \ -e 'SERVER_ADMIN_EMAIL' ='test@gmail.com' \ -e 'SIGNUPS_ALLOWED' ='false' \ -e 'INVITATIONS_ALLOWED' ='true' \ -e 'WEBSOCKET_ENABLED' ='true' \ -e 'ADMIN_TOKEN' ='eSLg6ZvXUjcd87Oiq2MRpTJEb0uODm4doh/RJSYi+GQeV7tCs+GP8l/98EEQ8mYf' \ -p '8086:80/tcp' \ -v '/opt/docker-data/vaultwarden/data' :'/data' :'rw' 'vaultwarden/server:latest'
2、配置 /home/ubuntu/dockerdata/letsencrypt/config/nginx/proxy-confs/password.subdomain.conf,password为将要使用的子域名,重启 letsencrypt 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 server { listen 443 ssl; listen [::]:443 ssl; server_name password.* ; include /config/nginx/ssl.conf; client_max_body_size 128M ; location / { include /config/nginx/proxy.conf; resolver 127.0.0.11 valid=30s ; set $upstream_app vaultwarden; set $upstream_port 80 ; set $upstream_proto http; proxy_pass $upstream_proto ://$upstream_app :$upstream_port ; } location /notifications/hub { include /config/nginx/proxy.conf; resolver 127.0.0.11 valid=30s ; set $upstream_app vaultwarden; set $upstream_port 80 ; set $upstream_proto http; proxy_pass $upstream_proto ://$upstream_app :$upstream_port ; proxy_set_header Upgrade $http_upgrade ; proxy_set_header Connection "Upgrade" ; } location /notifications/hub/negotiate { include /config/nginx/proxy.conf; resolver 127.0.0.11 valid=30s ; set $upstream_app vaultwarden; set $upstream_port 80 ; set $upstream_proto http; proxy_pass $upstream_proto ://$upstream_app :$upstream_port ; } }
-e ‘SIGNUPS_ALLOWED’=’false’ \ #不能注册
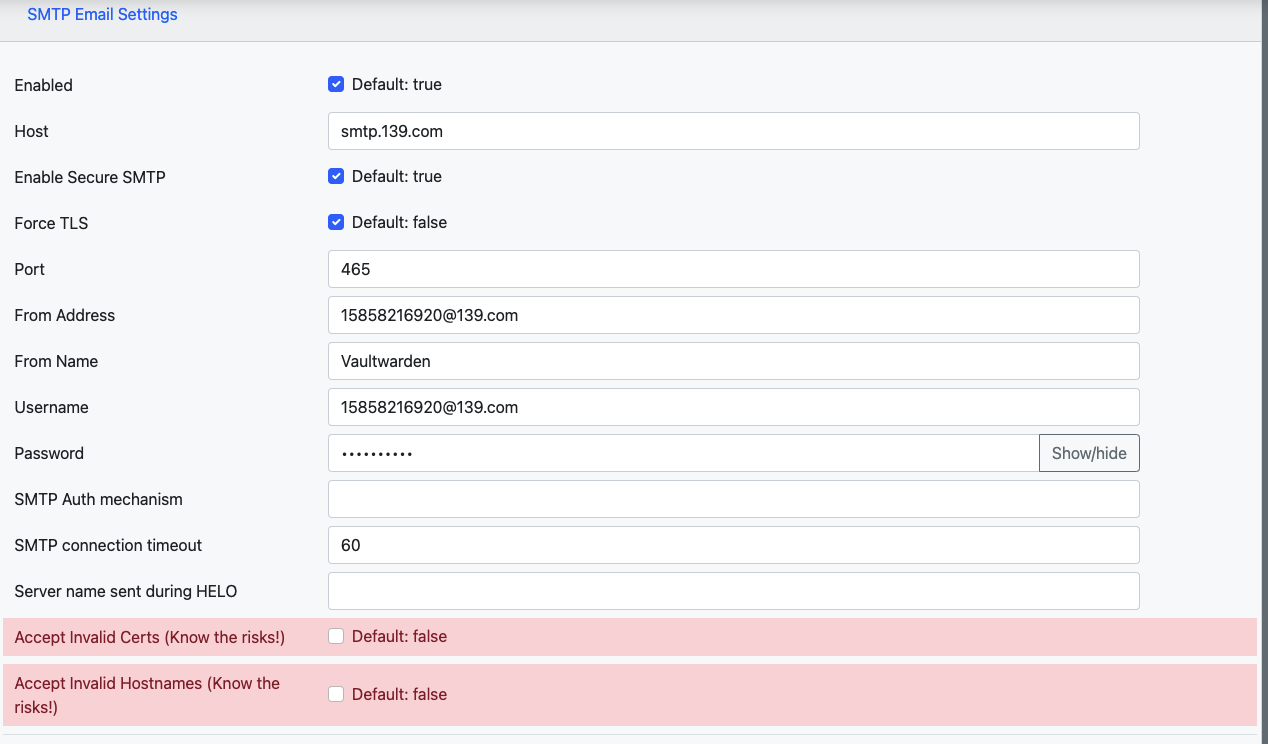
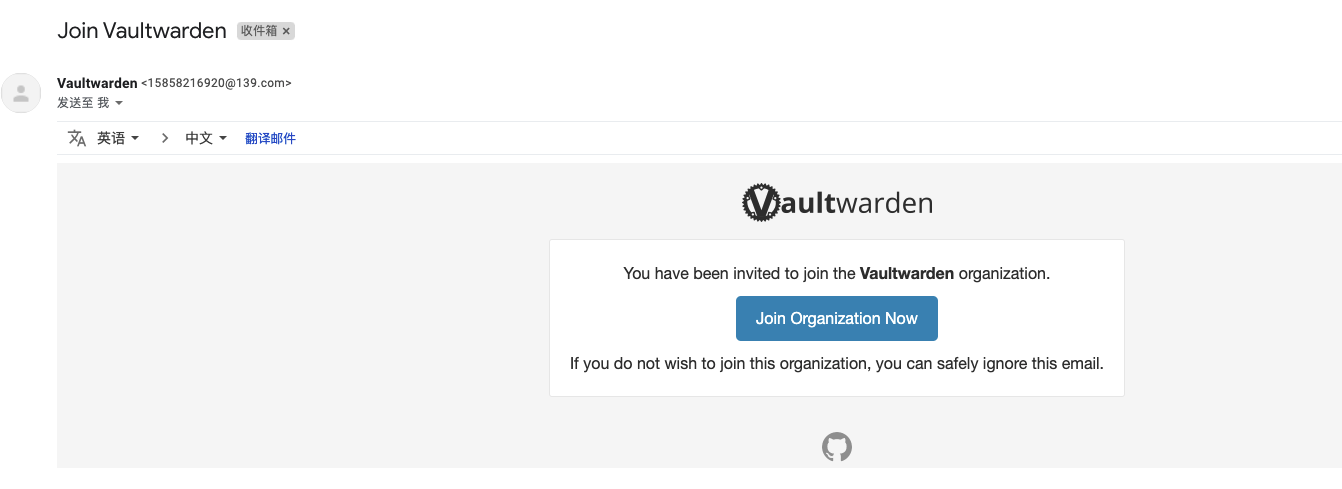
要成功发送邀请邮件,需开启邮箱的SMTP功能
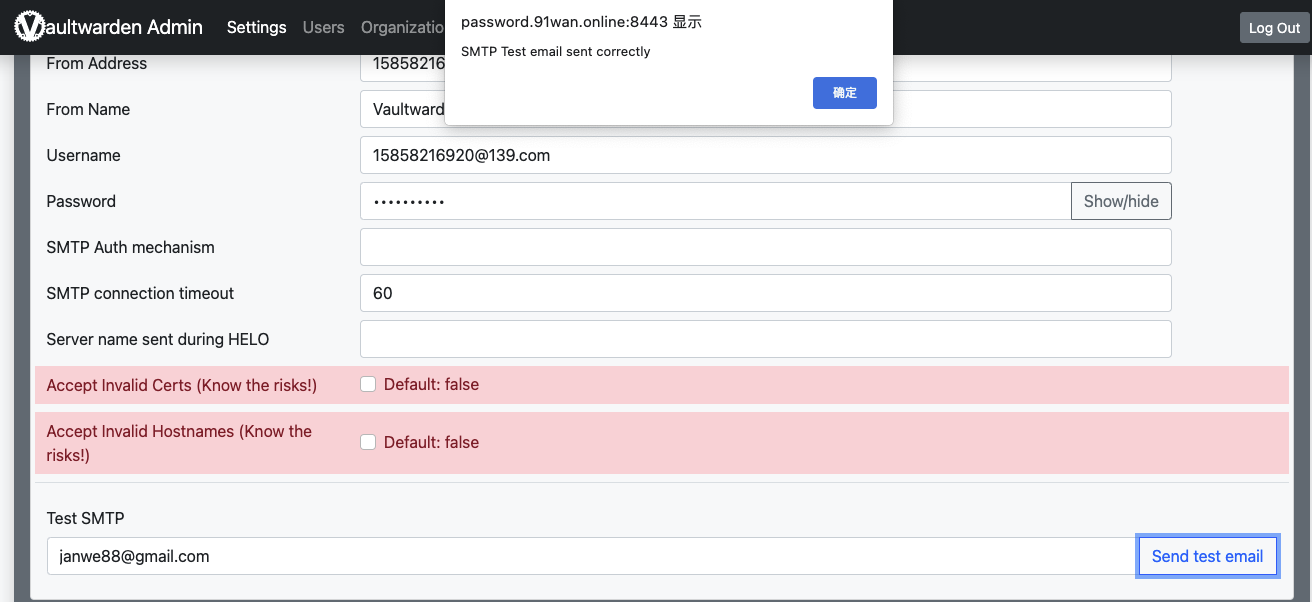
配置好后先保存,再发送测试邮件
4、测试成功后发送邀请
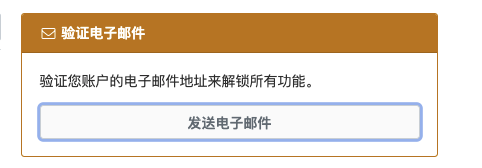
5、接受邀请并完成注册
6、开启两步登录
转载请注明来源,欢迎指出任何有错误或不够清晰的表达。可以邮件至 xiyugee@qq.com